Forget the Flu; Mark Gasson Fights Infection From Computer Virus

As the age of technology wears on, more and more people have been considering implanting themselves and their pets with chips that store information and communicate various details to other receptive technology. But skeptics wonder if it’s naive of people to consider such trends as simple and safe. What happens, for instance, when your information is hacked, when there’s a glitch in the technology, or when there chip catches a computer virus?
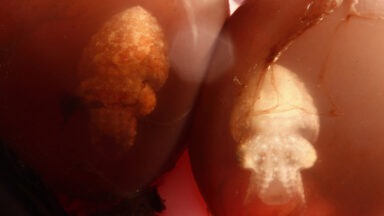
In 2009, Dr. Mark Gasson tested these reservations were tested at the University of Reading, by having an RFID chip implanted into his hand. Then, quite intentionally, he infected himself with a computer virus.
RFID Insertion
RFID stands for radio frequency identification and work like barcodes within a type of tracking system, transmitting information to a reader through radio waves. Although their original use was for merchandise, people have begun inserting them into their pets and even themselves.
If this sounds a little like the premise of a dystopian sci-fi where the protagonist is running from an authoritarian force that can track him anywhere, you’re not far off. The chips have already been used to locate missing people — for better or worse. On the plus side, Alzheimer’s patients who’ve wandered far from home can be found and returned, and victims of kidnapping incidents are more likely to be rescued.
However, the problem with this marriage between living forms and technology — what one might refer to as transhumanism — surfaces when, say, stalkers or criminals have the technology to find you, wherever you are. Their victims become easy to locate and target.
University of Wisconsin-Milwaukee sociology professor Noelle Chesley is among the critics of the RFID chip. She has expressed concern that chips may become mandatory for everyone at some point in the future. Along with vaccinations and other medical procedures, perhaps the day will soon come when infants routinely receive an rfid chip before leaving the hospital.
The problem with technology is complex these days. It seems that for every innovation, there is a dark side that exploits and misuses it. Cyber hackers have advanced as fast as technology, and most of the time, it’s nothing personal to them — they don’t necessarily want to harm you physically; they just want control over your information. And it’s not only hackers with this mentality; we are already seeing it with corporate giants and social media sites that dredge untold volumes of information from online databases, using it to market us to the extremes.
Such Orweillian ideas are already at our doorstep. While they do not sit well with some people, others, including Dr. Mark Gasson, willingly test the limits of RFID technology.
Dr. Mark Gasson’s RFID Experiment
One of the concerns with any computerized pieces of technology is the dreaded virus. We have already experienced massive viral attacks through the internet and seen how they easily disrupt our workflow, destroy our data, and cost us dearly in time, effort, and money.
According to an article by CSOonline.com, “a virus is deployed by attackers to damage or take control of a computer. Its name comes from the method by which it infects its targets. A biological virus like HIV or the flu cannot reproduce on its own; it needs to hijack a cell to do that work for it, wreaking havoc on the infected organism in the process. Similarly, a computer virus isn’t itself a standalone program. It’s a code snippet that inserts itself into some other application. When that application runs, it executes the virus code, with results that range from the irritating to the disastrous.”
Webroot, a company that harnesses the cloud and machine learning to predict and protect against cyberattacks, explained, “Designed to replicate relentlessly, computer viruses infect your programs and files, alter the way your computer operates or stop it from working altogether. While tens of thousands of computer viruses still roam the internet, they have diversified their methods and are now joined by a number of malware variants like worms, Trojans, and ransomware.”
Wondering what would happen if one of these RFID chips became infected by a virus, Dr. Mark Gasson, a cybernetics expert, decided to experiment on himself. The tag he used was similar to that which a person might implant into a pet; it was meant to help him walk through security doors and unlock his mobile phone.
When Gasson infected his chip, he first noted that when the computers in his lab read the code containing the virus, the virus spread to their databases and began to replicate. Afterward, when any of his colleagues attempted to enter the lab through their chips, the virus would be passed onto them as well.
The experiment proved a powerful point — that one person with an infected chip could take down an entire system. And when that chip becomes a part of someone by means of insertion into the body, and when society becomes dependent on such technology, great challenges lie ahead for all of us.
Major corporations that invest millions of dollars into cyber security still have their systems hacked regularly. Imagine what this would mean for a nation of chipped people if they were hacked by political adversaries — or worse, by a hostile enemy or corporate giant?
What does the human computer virus mean for the future?
Even though cyber security risks have not been settled, technological visionaries are dreaming up uses for chip technology being manifested by teams of experts — ideas that would literally affect people’s brain function — effectively making them cyborgs.
Elon Musk’s Neuralink is an example of one of the first brain-altering technologies of its kind, meant to be implanted into a human. Inventors and users of the technology hope to implant human brains with “threads” that can be used to alleviate such problems as brain disorders or to help a paralyzed person regain mobility. But imagine the repercussions if those chips were hacked.
We are in an era where the consequences of introducing even the best technologies pose a serious risk to the individual, societies, nations, and even the entire world. Critics of technology such as RFID chip argue that we have to carefully consider the cost of convenience, especially when it is being offered by third parties who have tapped into our private lives and, literally, our bodies.
A New Phase of Matter Appears to Defy Laws of Thermodynamics

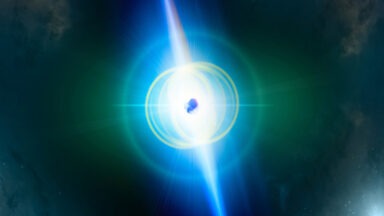
Scientists have created a new phase of matter known as time crystals, a quantum phenomenon appearing to defy the laws of thermodynamics. Could this discovery upend our understanding of classical physics?
A team of researchers developing Google’s Sycamore quantum computer announced the successful creation of a time crystal that lasted for 100 seconds. This novel phase of matter appears to defy the second law of thermodynamics, which states that entropy, or chaos and disorder, always increases in an isolated system. In other words, energy must be put into a system in order to maintain structure or motion. But time crystals have been observed to maintain a constant state of flux, without losing any energy.
Dr. Simeon Hein, director of the Institute for Resonance, explains the science behind this strange phenomenon.
“Crystals are in everything we do—they’re in watches—they’re in so many things because they’re regular, they create evenness, they create this consistency. And just like their pattern is very consistent, the energy that crystals transmit turns into a very regular pattern which is why you can use a quartz crystal in a watch,’ Dr. Hein said.
“You can put a noisy electrical signal in but it will come out as a very consistent beat, and that created the idea for some people, in this case, Frank Wilczek from M.I.T. in 2012, to propose the idea that you not only had crystals in space, you could have crystals in time. You could create an oscillating circuit, using specific quantum principles, you could create a very constant quantum beat.”
Time crystals have been described as the first “out-of-equilibrium” phase of matter, meaning they maintain order while in an excited state. But how do time crystals accomplish this, without expending energy?
“At a quantum level, they’re getting energy from something called the Zero-point energy field. The Zero-point energy field is the lowest ground state of quantum matter, but the lowest state doesn’t mean absolute zero like nothing’s happening. The quantum ground state is actually the base state of the universe, where even though there’s nothing happening, the field itself generates energy, causing random fluctuations and particles to pop out of nowhere, and all sorts of really interesting effects that normally, I should say most of the time, we don’t see in our regular, physical reality,” Dr. Hein said.
“So these coherently entangled particles would be deriving their energy from the quantum vacuum field. But if they’re getting their energy from the quantum vacuum, instead of our classical world, you can’t see any reason why they would eventually have to wind down like our regular clocks would, and energy would dissipate.”
With this new discovery of time crystals appearing to defy the second law of thermodynamics, how has mainstream science reacted, or tried to reconcile this paradox?
“A lot of these quantum phenomena seem to defy classical physics, the whole idea of quantum entanglement suggests faster than light interaction or communication, Einstein called it ‘spooky action at a distance,’ and experiments later confirmed that you could take pairs of particles and separate them, and you could do something to one of them, and the other particle would immediately react at farther and farther distances away,” Dr. Hein said.